NYC Resistor was mentioned in "The New York Times" today. My favorite part of the article was where Diana Eng, booted from "Project Runway" because her designs involved electronics, sounded like Charlie, the jack-in-the-box from The Island Of Misfit Toys:
“My designs were too nerdy for ‘Project Runway,’ ” Ms. Eng said with a giggle. “But here they fit right in.”
Check out the full article:
http://www.nytimes.com/2008/12/28/nyregion/thecity/28tink.html
Sunday, December 28, 2008
Sunday, November 30, 2008
Cathedral of ST John the Divine Rededication


What's a Mennonite doing in an Episcopal Cathedral? Filming speakers Senator Hillary Rodham Clinton and Senator Chuck Schumer, what else? The Cathedral Church of ST John the Divine held a rededication today after 7 years of restoration from a devastating fire. What a wonderful service! One of the highlights of the service for me was when Dean James A. Kowalski introduced Senator Clinton by stating, "Will she be our Senator for long, you wonder?" Even for a church, the crowd couldn't contain themselves. My other highlight was when Dean Kowalski made reference to "another great Cathedral that we paid homage to this year, Yankee Stadium!"
Senator Chuck Schumer harkened back to the first dedication of the cathedral which happened on this very date of November 30th, 1941.
Also in attendance were Cardinal Edward Egan, New York's Roman Catholic Archbishop, and I even spotted Bishop Noel Chin, District Superintendent of New York's United Methodist Metropolitan District in the crowd. Former Mayor David Dinkins was there as well.
Monday, October 27, 2008
Keeping Your Kids Safe Online: What Every Parent Needs To Know

I was invited to give an online safety presentation to parents of Police Athletic League kids. I have posted it online in hopes that others will find it helpful. I'm tentatively slated to give this workshop again, early next year (2009).
Wednesday, October 15, 2008
What Happens In Vegas?

What’s a Mennonite doing in Vegas? Facilitating for the SANS Digital Forensics and Incident Response Summit, what else? I actually arrived in Vegas a few days early to gain some additional training, taking the SANS Browser Forensics and Digital Analysis classes from the incredibly talented Mike Murr.
As always at SANS, I learned a ton. My personal take-aways from the summit, and almost themes if you will, were two resounding messages: (1) Pulling the plug on “pulling the plug” and (2) Don’t neglect your points of egress (or what I like to call, don’t let the door hit you on the way out!).
Steven D. Shirley from DC3 gave the opening address, and Rob Lee was the Chair.
It seemed almost every presentation mentioned that pulling the plug in an IR investigation is dead! After all, isn’t Incident Response often about “live” acquisition? To that end, the significance of memory forensics played front-and-center-stage during many of the presentations, with guru AAron Walters leading the charge.Eoghan Casey (pronounced Owen) and Chris Daywalt reminded us that what leaves our network is critical, and that creating a baseline or “white list” for our points of egress is paramount. We were also advised to baseline our network traffic, and our system’s memory. We were cautioned that we might not want to become complacent inside the “soft and chewy center” of our WAN. If we become lazy or get too comfortable with our “trusted” core, we could very well be leaving ourselves wide open. Being a skeptical New Yorker, when I write about trust, I like to break it into three categories: (1) blind trust, (2) no trust, and (3) earned trust. Blind trust is obviously unsafe, trust no one is preferable (in my opinion) but highly unpractical in the real world, and earned trust isn’t utopia, but deserves some merit.
We also reviewed some necessary basics that are still being overlooked by many:
●Naming conventions, i.e., instead of naming our boxes by their function, choose a less pronounced schema. I’ve seen corporations use fantasy characters or even types of beer.
●Don't allow "mount shares" on domain controllers.
●Allow a minimum of 30 minutes each day to review logs (of course we’d prefer more, but this is preferable to zilch). And if you notice, for example, in your VPN logs that you have 40 minutes worth of attempts at $ or root, you might want to take a closer look.
●Stay away from i-frames on your web pages.
●Make all users non-admins. I will warn you that without the support of upper management, this could backfire. If you are upper management, support it 100%, and have a policy in place. A common argument against this is that the business culture doesn’t support it, or it’s not practical. For a lot of us in security, this is 101, which is why it may be hard for some of us to fathom, but this small decision has the potential to create many enemies. Just try taking away the CEO’s privilege to download music, yet how many times have we seen some of the biggest offenders against our network policies coming across the wire that leads straight to the jack next to the mahogany desk.We learned about the increasing importance of preparing for a breach. I’ve referred in the past in this blog to learning at SANS that the minute we think our network is secure, is the second we’ll be hacked. Ego often plays a role in network security, but it’s almost tabu to draw attention to it. Perhaps it’s time we check our ego’s at the door of our Data Centers, and devise a contingency plan in the unfortunate event that we ourselves suffer a compromise.
Steve Whalen of Forward Discovery walked us through iphone forensics-Awesome! Ovie Carroll (I love my scarey t-shirt!) spoke about “User Attribution” and that finding the smoking gun isn’t enough. We must be able to connect the dots from that gun, using fingerprints, GPS, text message logs, recent e-mails, phone calls and even Google Searches. A thorough digital investigation has to be a combination of good-old law enforcement investigation skills, mixed with a deep-dive into the events leading up to (and from) the crime scene.Richard Bejtlich (pronounced “Bait-Lik” by the way for those who have the opportunity to meet him for the first time and don’t care to mispronounce his name) echoed some of the same challenges about building and deploying security best practices that we had just heard at our most recent NYC InfraGard meeting from David Stern of DoITT, who oversees many of NYC’s finest concerns. Mr. Bejtlich used the example of building a bridge and how the Safety Inspector is told to “go away” because they need to finish the project by January first and that all the Inspector is doing is slowing things down. Then when the bridge collapses, they yell at the Safety Inspector, chiding him and asking him why he hadn't ensured their safety.Harlan Carvey, a veritable rock star, walked us through registry analysis. Clearly he has way too much fun with reg keys, leaving all of us to reap the many benefits.
Verizon's CyberTrust group was represented, and their well-received Data Breach Investigations research paper was brought up on more than one occasion. We were also made aware of an addendum to that paper.
The entire summit was a slam-dunk, right up to the final session. It was a "shoot-out" with Chris Brown, CEO of Technology Pathways (ProDiscover), Gus Quiroga, Product Manager at Guidance (EnCase) and Matthew Shannon, Founder F-Response. I wanted to jump up and down when the question was raised asking each vendor what they were planning to give-back to the community, and I was very impressed by each of their responses. ProDiscover has a free version of their software (if I remember correctly when I first used it, it is limited to the number of times you can us it), but it does not have a number limitation on artifact ingestion. The others offer sliding scale prices for law enforcement and education.
I highly recommend this event, and am personally signing up again for the next SANS Digital Forensics & IR Summit that I’m told will be held in DC in July of 2009 (less than a year to have to wait-hurray!).
Saturday, September 27, 2008
The Last Hope Conference

It’s been a busy summer and I’m just now posting on some of the conferences that I attended. Everyone enjoyed The Last Hope, and we are now looking forward to The Next Hope!
Here are some links from the talks that I attended. You can catch recordings of all of the HOPE talks over at The Last Hope Web site. There were many presentations that I wished I could have attended, however the conference had three tracks running simultaneously, plus an ad-hoc fourth track, and I haven't yet figured out how to hack myself. Some of the talks were repeated the following week at DefCon.
The (Im)possibility of Hardware Obfuscation
By Karsten Nohl
This talk was incredible, and set the pace for the rest of my conference experience.
The MBTA subway hack paper by a group of MIT students is related, so I have posted a link here. Is NYC susceptible to this same vulnerability? The next NY Metro InfraGard meeting will be held at MTA Headquarters, and will focus on physical security. I’m hoping to contribute.
Maintaining a Locksporting Organization and Breakthroughs in the Community
By Doug Farre, Jon King
http://www.locksport.com
Watch rock star Jon pick a Medeco lock using his “Medecoder” tool.
Citizen Engineer - Consumer Electronics Hacking and Open Source Hardware
By Phillip Torrone, Limor Fried
In her presentation, Limor dissected a retired public telephone and turned it into her home phone. Very cool. I recommend her cell phone forensics kit. Also, if you’ve heard about the mp3 player made out of an Altoids tin, it too was a project of Lady Ada.
http://www.adafruit.com
The Attendee Meta-Data Project
By LexIcon, Daravinne, Neo Amsterdam, Aestetix, Echo, Dementia, Matt Joyce, Christopher Petro


I didn’t actually make it to this one, but like so many of the presentations that I didn’t make it to, it really interested me. I’m streaming the audio online as I type, and according to the audio, they had enough of these special RFID badges to fit about half the number of attendees. Those people were then viewed as objects in a “live” database--sort of like social networking on crack, and general crowd movement could be tracked, for example congestion around the elevators or certain vendor tables.
http://amd.hope.net/
http://www.OpenBeacon.org/attendee-meta-data-project.0.html
http://www.bitmanufaktur.de/
Wikipedia: You Will Never Find a More Wretched Hive of Scum and Villainy (Partial)
By Virgil Griffith
I really just caught the last 5-10 minutes of this one, but it created quite a buzz.
http://www.WikiWatcher.com
http://virgil.gr
http://wikiwatcher.com/WikiWatcher_HOPE.pdf
http://vispedia.stanford.edu
http://graphics.stanford.edu/projects/vispedia
Introduction to MCU Firmware Analysis and Modification with MSP430static
By Travis Goodspeed
I wanted to catch this one as it seemed interesting and he’s a friend-of-a-friend, but didn’t quite make it.
Introduction to the Open Web Application Security Project (OWASP)
By Tom Brennan
OWASP is home to WebGoat and many other wonderful projects. I just attended their NYC conference and will post that information as time allows.
Advanced Memory Forensics: Releasing the Cold Boot Utilities
By Jacob Appelbaum
Autonomously Bypassing VoIP Filters with Asterisk: Let Freedom Ring
By Blake Cornell, Jeremy McNamara
http://www.SecurityScraper.com
http://www.Jeremy-McNamara.com
A Collaborative Approach to Hardware Hacking: NYCResistor (Partial)
By Bre Pettis and Friends
I support NYC Resistor and find the group a really welcoming bunch.
Technical Surveillance Countermeasures (Electronics Surveillance and Bug Detection)
By Marty Kaiser
Marty Kaiser has been involved with digital security and surveillance for as far back as most of us have memory. Listening to Marty was like hearing an old-fashioned radio show, filled with great stories. He brought up the infamous Russian Seal Bug, which is a fascinating piece of history. I could have spent the rest of the day just listening to more pieces from his past (and present) experiences.
A Convergence of Communities
By John Strauchs
Mr. Strauchs touched on something that’s increasingly important: IT Security + Physical Security. Can you have one without the other? His talk reminded me of an RFID crack that I’d heard about recently. It’s by Chris Paget at IOActive, Inc. This was not part of the HOPE Conference, but it’s tangentially related, so I thought it worth mentioning. View a video demonstration of Chris using the device here.
Crippling Crypto: The Debian OpenSSL Debacle
By Jacob Appelbaum, Dino Dai Zovi, Karsten Nohl
Wow!
http://trailofbits.files.wordpress.com/2008/07/hope-08-openssl.pdf
http://wiki.debian.org/SSLkeys
http://www.debian.org/security/key-rollover
http://blog.trailofbits.com/2008/07/21/crippling-crypto-the-debian-openssl-debacle
http://wiki.debian.org/SSLkeys
http://www.debian.org/security/key-rollover
http://blog.trailofbits.com/2008/07/21/crippling-crypto-the-debian-openssl-debacle
Keynote Address
By Steven Levy
By Steven Levy
Methods of Copying High Security Keys
By Barry Wels, Han Fey
I won a lock-pick at this very interesting presentation.
http://www.toool.nl
http://www.toool.us
Port Knocking and Single Packet Authorization: Practical Deployments (Partial)
By Michael Rash
Bagcam - How Did TSA and/or the Airlines Manage to Do That to Your Luggage?
By algormor
These videos are a must-see!
Featured Speaker
Steven Rambam
Basically this guy’s a PI on crack, brilliant! And if you ever need to track someone down, he will find them.
Part 1
Part 2
http://video.google.com/googleplayer.swf?docid=2219573359400519690&hl=en&fs=true
Social Engineering
By Emmanuel Goldstein and Friends
One ploy involved Emmanuel phoning a luxury hotel in NYC (Ritz Carlton?) and confirming their bed-bug eradication assignment in the morning.
Social Engineering
By Emmanuel Goldstein and Friends
One ploy involved Emmanuel phoning a luxury hotel in NYC (Ritz Carlton?) and confirming their bed-bug eradication assignment in the morning.
Featured Speaker
Kevin Mitnick
Kevin Mitnick
Kevin Mitnick handed out his ingenious business card that doubles as a lock-picking set to the first few hundred who lined-up after he spoke. I remember way back when, working at one of the few isp’s in NYC. The choices were pretty much PANIX or ECHO. I worked at ECHO for Stacy Horn, and Kevin did too. The rest, they say, is history.
http://video.google.com/googleplayer.swf?docid=417390258297273732&hl=en&fs=true
PenTest Labs Using LiveCDs
By Thomas Wilhelm
Mr. Wilhelm is a genius and wants to share everything he has learned with everyone. His generosity and attitude is infectious. I highly recommend downloading his lab.
PenTest Labs Using LiveCDs
By Thomas Wilhelm
Mr. Wilhelm is a genius and wants to share everything he has learned with everyone. His generosity and attitude is infectious. I highly recommend downloading his lab.
Pen Testing the Web with Firefox
By DaKahuna & theprez98
Identification Card Security: Past, Present, Future
By Doug Farre
How to craft your own holographic IDs.
https://www.defcon.org/images/defcon-16/dc16-presentations/defcon-16-farre.pdf
Programming Your Mobile Phone for International Calling
By The Cheshire Catalyst
Programming Your Mobile Phone for International Calling
By The Cheshire Catalyst
I didn’t catch this one, but Cheshire sent me some of his own links from the conference that I thought were handy.
Warrantless Laptop Searches at U.S. Borders
By Decius
http://wwwHandsOffMyLaptop.org
http://www.memestreams.net/search/?search=laptop
YouTomb - A Free Culture Hack (Partial)
By Oliver Day, Dean Jansen, Quentin Smith, Christina Xu
I didn’t catch all of this one, but what I did grab was quite interesting. Here’s a blurb from their site:
“YouTomb continually monitors the most popular videos on YouTube for copyright-related takedowns. Any information available in the metadata is retained, including who issued the complaint and how long the video was up before takedown. The goal of the project is to identify how YouTube recognizes potential copyright violations as well as to aggregate mistakes made by the algorithm.”
Postal Hacking
By CypherGhost
I’ve included the above video link to a different presentation that he gave, but there was some overlap. This was quite an entertaining talk.
Strengths and Weaknesses of (Physical) Access Control Systems
By Eric Schmiedl, Mike Spindel
This talk was very engaging. The example of using yellow high-lighter pen (blends in on keypad) on your finger to track the order on a keypad (under uv lighting) was an interesting concept.
No-Tech Hacking
By Johnny Long
The icing on the cake. Pure fun!
http://Johnny.iHackstuff.com
http://www.HackersForCharity.org
This next (and last but NOT least) link is not from HOPE, but was released at DefCon from a colleague of mine, Kevin Johnson. I thought it fitting to include. It’s a “Live” Web Penetration Testing CD called Samurai. Some of you know Kevin better as The Hacker Princess…Long live the princess!
Tuesday, September 9, 2008
Self-Defense Seminar For Women

My Kung Fu school is offering a six-week, hands-on training course geared toward women's self defense. Our current students range from school teachers, to active law enforcement. I remember being present at an awards ceremony and hearing testimony from one of New York's finest who stated that it was because of the defense tactics taught in this school, that they were still alive.
This is a great opportunity to learn some very effective skills, in a safe and friendly environment. I personally know Sifu Yui Chow to be one of the most dedicated and considerate teachers I've ever been privileged to learn from. Click on the picture above for more information.
Saturday, August 16, 2008
Mennonite Hacker?
I recently spent a couple of days visiting some of my Amish friends and Mennonite relatives. I find this video comical as I'm attempting to explain my line of work to some of my Mennonite relatives.
Wednesday, August 6, 2008
Is My Child Safe Online?
Since attending the CyberBullying Conference, and being approached by Nickelodeon about the safety of kids online, I’ve decided to put up a few helpful links for parents who may be asking, “Is my child safe online?”
● Parry Aftab, online safety guru; her Web site is the single most comprehensive collection of online safety tips for kids.
● The FBI offers a very helpful parental online guide
● Consumer Reports offers a useful guide to kid’s online safety
● PBS FrontLine documentary Keeping Kids Safe Online
● NY Times columnist David Pogue takes a practical approach
● NY Times columnist Harlan Coben offers a tough-love scenario
● Read through danah boyd’s blog postings on Youth Culture
● Parent-child online agreement
● Parry Aftab, online safety guru; her Web site is the single most comprehensive collection of online safety tips for kids.
● The FBI offers a very helpful parental online guide
● Consumer Reports offers a useful guide to kid’s online safety
● PBS FrontLine documentary Keeping Kids Safe Online
● NY Times columnist David Pogue takes a practical approach
● NY Times columnist Harlan Coben offers a tough-love scenario
● Read through danah boyd’s blog postings on Youth Culture
● Parent-child online agreement
Friday, May 16, 2008
CyberBullying Conference

I'm honored to be participating in the upcoming CyberBullying Conference on June 2 and 3 in conjunction with PACE University and the one and only reknown/revered Parry Aftab. To learn more about cyberbullying, visit Parry Aftab's blog. Aftab was just on Good Morning America today discussing the Megan Meier and Lori Drew case with Tina Meier.
Tuesday, April 15, 2008
Boston Red-Tailed Hawks

Photo Credit: Globe Staff Photo/Stan Grossfeld (2008)
I've been commuting to New England quite a bit these days, and enjoying the change of scenery. They have hawks there as well. Unfortunately, there's been a Red-Tailed Hawk at Fenway Park that has been getting some negative press.
Monday, April 14, 2008
"Live" Owl WebCam!

Owls fascinate me. My favorite type are the big, fat, Great Horned Owls. Check out this incredible Owl Web cam, placed right on their nest! Watch it daily to see the youngin's fledge!
Tuesday, February 26, 2008
Microsoft HotMail Down and Out
Microsoft HotMail is down today, could be a router issue or maybe they got hacked...again. If so, it will be headlines tomorrow. If you have any updates, please post here.
Update: This just in from the SANS.org Internet Storm Center:
>>we have had multiple reports of issues with hotmail all over, going directly to the login.live.com site seems to work.<<
Works for me! And maybe we'll read in the papers, or see on the News tonight, what really happened.
Update: This just in from the SANS.org Internet Storm Center:
>>we have had multiple reports of issues with hotmail all over, going directly to the login.live.com site seems to work.<<
Works for me! And maybe we'll read in the papers, or see on the News tonight, what really happened.
Friday, January 25, 2008
CyberCrime Film

Just back from SANS Security in New Orleans, I jumped at the opportunity to hop on down to Tribeca for the premiere of a documentary, The New Face Of CyberCrime.
Being a skeptical New Yorker, I couldn't help but wonder if what we were about to view would be an infomercial for Fortify Software, the sponsors of the documentary, however, I was actually impressed with the short. They included a snapshot into the brilliant Marcus Ranum, and a very personal one-on-one with Myron Ullman, CEO of JC Penny, whom I thought was extremely eloquent. He offered-up a highly evolved approach to intrusion and penetration, one that I (having a martial arts background) sometimes refer to as, the Xing Yi approach. Plain and simple, it's the understanding that the minute you think your network is impenetrable, is the second you'll be hacked, a lot like the acknowledgement that even though one may be an accomplished martial artist, a bullet is a bullet. In my opinion, Ullman depicted the arbiter of a well done film, that someone so high profile was willing to be that candid, and that honest, admitting that they simply "don't want to be that headline."
Afterward, the filmmaker and some of those interviewed in the film were present and taking select questions from the audience. One of the panelists, a journalist, spoke volumes when he pointed out that the TJX incident would have had a lot less negative publicity, if the higher-ups had been more apologetic and more empathetic to their customers. Instead, they kept insisting on finger pointing. Great example, is the opposite happened when Bank Of America was breached and went out of their way to apologize publicly, promising their customers they would not be held liable, and in many ways raising the bar and setting the standard that others in that situation now follow.
The food and drinks after the film ROCKED, and my friend Bill, Chair of NYPC.org and I decided to end the evening by grabbing his new XO (One Laptop Per Child) notebook and head over to Starbucks to configure it for its one-year free wifi with T-Mobile. What we couldn't seem to figure out was the meaning behind the color schema for the different networks that appear as dots on the screen. I was guessing that blue denoted a Linksys router and perhaps silver was Netgear, but I later discovered that the color of the circle is based upon the name of the access point. What still isn't clear to me, is what about the name defines the color that your circle will be. If you know, please comment here!
Thursday, January 24, 2008
SANS Security New Orleans

Photo Credit: Kathy Northcutt/SANS Institute (2008)
Here's our facilitator team from my most recent SANS Digital Security bootcamp in New Orleans.
SANS Institute is to information security what Top Gun is to the Air Force. SANS travels all over the world, setting up bootcamp training in computer crime forensics, perimeter protection and wireless security, to name a few. Their instructors are hands down, the best of the best, the elite.
I have had the privilege of being a SANS facilitator, assisting the instructors at now three SANS bootcamps (Orlando, San Diego and New Orleans). My goal is to work at least 2 SANS events each year.

I was especially glad that I could attend the SANS bootcamp in The Big Easy. New Orleans has seen anything but easy these past couple of years, and it was great to contribute in some small way to the recovery of their economy. In addition to pumping hotel, airfare and meals into the local market, I managed to pull a few cranks on some penny slots and still have enough leftover for these lovely alligator oven mitts (above photo). Last time I was in New Orleans (2000?), I went on a guided swamp tour to see real gators in their natural habitat. One of my few regrets in life is that I didn't save the cloth alligator cap that I bought as a souvenir from that trip, but no time to go 'gatoring this go-round, this visit was 99% business! (If you're wondering where the other 1% went, you can go to my other blog, HackerPrincess.blogspot.com, guess you had to be there...)
Unfortunately the photos I took were from one of those instant cameras and either the one I purchased had gone through the flood, or the developer did something wrong, but the pictures came out extremely grainy and pixilated. Guess I'll just have to go back!


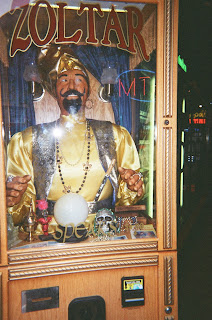
Ah, I see another SANS in your future!
Subscribe to:
Posts (Atom)




